Directed Energy Weapons Electronic Harassment & Remote Neural Monitoring
We have to see to it that global virtual war on around thousands of unarmed civilians in seven billion population comes to end as quickly as it can. There is excessive use of military grade, yet to come, technology on unarmed civilians. The perpetrator claims that they have remain invincible for three decades now, but I tell it is primarily due to use of military grade, yet to come, on unarmed civilians and that too in thousands in population of seven billion and that is reason of success. Probably starting from 1980s, this technology has outlived. Given the vast satellite monitoring, electromagnetic space monitoring by professionals and vast electronic warfare budget, this technology has probably survived due to its unprecedented electronics. A whistle-blower will be helpful, but in absence, the following can be tried.
No Government Agencies, Judicial Body or Human Right Activist body understand this problem. It has to be solved by handful of people who are targeted and some who believe in them.
Overall Objective :
The overall objective is to identify the satellites, who owns them, through spectrum analyzer and neurosky collect evidence to correlate satellite to brain interfacing. By knowing the satellite, classified or unclassified, we will be able to ascertain ownership.
Breakthrough in Evidence Collection – Magic of 1 Ft Wire!!
This video is breakthrough in getting RF hearing or voice in signal capture. Tom Lee captured RF Hearing signal using 1 ft wire as antenna and connected to FFT Spectrum Analyzer. Here is full video, must watch!! Read More: http://remoteneuralmonitoringindia.blogspot.com.au/
RNM Remote Neural Monitoring Satellite Terrorism
Being Harassed and Terrorized by RNM Remote Neural Monitoring
Private criminals or corrupt government are tapping into and somehow gaining access to Government satellite technology using RNM Remote Neural Monitoring also known as Satellite Terrorism and terrorizing individuals. This is being done illegally to individuals across the United States and these criminals are going unpunished. in many instances these criminals are using a Bogus illegal terroristic so called “investigation” once the satellite is locked on the individual this “investigation” is nothing more than repetitious harassment and terrorism to the victim that last for years and is meant to drive the victim insane commit suicide or have them jailed or institutionalized. Targets or victims should be aware that the definition of paranoid schizophrenia as “amended”, includes victims references to voices and the belief that someone’s reading/controlling their mind. Although, current technology allows this and illegal experiments to involve the remote causation of all these “symptoms”. The psych bibles such as the DSM-IV do not contain that “classified” information. This is so that psychiatrists can be used to discredit victims by joining them with those who have a genuine condition. Long term unemployment, isolation and other social problems also fit the psych profile of schizophrenics but, again, most victims of technology crimes finish up in the same position and so can easily be confused with those having the disorder. Read More: http://satelliteterrorism3.blogspot.com.au/2010/12/dew-directed-energy-weapons.html
There has been a new development in the Remote Neural Monitoring. As
mentioned previously, I have been able to successfully block the signal
using a Faraday cage, but unfortunately this technique only blocks part
of the signal (the audio component). Having already made them aware (how
can I help it) that I now possess the know-how to build a device to
record the audio component:
1. Capture the microwave signal at 300-400Mhz range. I don’t know what
exact electromagnetic frequency they are using but it is at the range
when the waves will behave partly as microwaves and partly as radio
waves. As mentioned previously, it requires a complete body enclosure in
the Faraday cage to block the audio component since the human body acts
as an antenna so covering the head alone is not sufficient.
2. The microwave signal uses FM modulation to encode the audio
component, when it hits the skin it creates an internal 10Hz – 15Hz and
20Hz subsonic wave which interacts with the brain’s own bio electrical
systems. The different wavelengths allow them to interfere with the
auditory, visual cortex and somatic systems of the brain respectively.
There are already devices on the market that:
1. Create hallucinations by generating signals at these wavelengths
(they are marketed for recreational purposes).
2. Allow you to talk with your brain to a telephone by simply attaching
the device to your skin.
In order to record the audio signal, one requires a receiver capable to
tuning in to the appropriate microwave range. No a regular radio will
not do.
You then need to use an FM demodulator to extract the sounds, increasing
the pitch to a level to which they can be heard by the human ear.
The video component is a bit more of a challenge though. The fact that
it can get through the Faraday cage means that it is Far-InfraRed
(1mm/1000um) or Thermal-Infrared (100um) wavelength – so the traditional
means to blocking microwave radiation will not work.
It makes sense that to create the 10-15-20Hz sounds on impact a
different electromagnetic frequency needs to be used.
So what have they done?
They have turned off the audio component but maintained the video
interference. Mainly because they know that it is within my means to
record them now.
I will do some more research on how to capture or block far and thermal
infrared signals.
From a philosophical standpoint, the universe is a balanced God – while
this “exploit” into the human mind seems to go against everything we
believe is holy with regards to human rights, even the average
individual, given the appropriate knowledge has the means to fight back
against the atrocious technology.
A final note. So far, my actions have been defensive and defensive
alone. There is a third and final solution, one which I am loathe to
undertake because doing so would make me just as bad as these people.
Sending a microwave or infrared jamming signal, rendering all attempts
to monitor my brain both futile and PAINFUL. Source: https://groups.google.com/forum/#!topic/soc.culture.australian/qYSrfY5NdUQ
Remote Neural Monitoring: How They Spy on Your Thoughts
All of us have been through this process, and the new and improved technologies being developed around the world, supposedly to deal with crime and terrorism, and inadvertently intrude on one’s privacy, should probably bring us all to the brink of paranoia.
These technologies are funded by governments at the highest level and some of the countries involved includeUSA, UK, Spain, Germany and France.
Recently, the infamous National Security Agency (NSA) of the U.S.A. has developed a very efficient method of controlling the human brain.
This technology is called Remote Neural Monitoring (R.N.M.) and is expected to revolutionize crime detection and investigation.
R.N.M. works remotely (ever wondered why have we all been driven relentlessly towards wireless systems?) to control the brain under the objective to detect any criminal thought taking place inside the mind of a possible culprit. Inevitable question: How can you isolate a criminal thought if you do not have a comparative measure of non-criminal thoughts?
This undertaking is based on two principles:
- The research studies have shown that the humanoid intellect thinks at a speed of about 5 kilobits per second and, therefore, does not have the capability to contest with supercomputers acting via satellites, implants and biotelemetry.
- The human brain has a characteristic set of bioelectric resonance structure. By using supercomputers, the R.N.M. system can home in on it, and send messages through an embedded individual’s nervous system in order to affect their performance in a preferred way.
The entire system has been developed after about 50 years (!) of neuro-electromagnetic human experimentations, claimed to be involuntary, but there is no evidence to support this claim. According to many scientists involved in this program (their names are not revealed for obvious reasons), within a few years it is expected that DNA microchips, under the guise of medical breakthroughs that will be presented to launch the disease cure processes on speed and efficiency, will be implanted in the humanoid cereberum, which would make it inherently controllable. R.N.M. will then have the ability to read and govern a person’s emotional mental procedures along with the involuntary and visions.
At present, around the world, supercomputers are watching millions of people at the same time, with the speed of 20 terabits per second, particularly in countries like USA, Japan, Israel and a number of European countries. A similar program is supposedly under way in Russia.
How does R.N.M. work? It employs a set of programs functioning at different levels, like:
- The signals intelligence system which applies electromagnetic frequencies (EMF), to excite the brain for the system and the electronic brain link (EBL).
- The Brain Stimulation system that has been planned as particle emission intelligence, which means receiving information from unintentionally created electromagnetic waves in the environment. However, it is not related to radioactivity or nuclear detonation.
- The recording machines that have electronic equipment to examine electrical action in human beings from afar. This computer-generated brain charting can always record all electrical events in the cerebrum.
- The recording aid system deciphers individual brain maps for security purposes.
The underlining technology of this system takes under consideration that the electrical activity in the speech center of the brain, can be translated into the subject’s verbal thoughts. R.N.M. can send encrypted signals to the audio cortex of the brain directly circumventing the ear. This encoding assists in detecting audio communication. It can also perform electrical mapping of the cerebrum’s activity from the visual center, which is achieved by avoiding the eyes and optic nerves, consequently projecting imageries from the subject’s mind onto a video display. With this visual and audio memory, both can be visualized and analyzed.
The machinery involved can, remotely and non-invasively, detect information by digitally decoding the evoked potentials in 30-50Hz, 5 mW electromagnetic emissions from the cerebrum. Evoked potentials are called the spikes and patterns created by the nerves, as they produce a shifting electrical pattern with an ever-changing magnetic instability, which then puts on a constant amount of electromagnetic waves. The interesting part about this is that the entire exercise is carried out without any physical contact with the subject.
The EMF emissions can be decoded into current thoughts and audiovisual perception, in the subject’s gumption. It sends complicated cyphers and electromagnetic pulse signals to activate evoked potentials inside the mind, consequently generating sound and visual input in the neural circuits. With its speech, auditory and visual communication arrays, R.N.M. allows for a comprehensive audio-visual mind-to-mind connection or a mind-to-computer association.
The mechanism needs to decrypt the resonance frequency of each specific site to modulate the input of information in that specific location of the cerebrum.
See also: Mind Control 101: The Basics
Furthermore, R.N.M. can detect audio via microwaves, and features the broadcast of precise directives into the subconscious, producing visual disorders, illusions and instillation of words and numbers into the brain through radiation waves.
With all the given paybacks for tracing the unlawful and traitorous activities,there are many alarms and dangers being pointed out by human rights advocates and scientists. The agencies of human rights, worldwide, have criticized the system as an affront to the basic human rights because it violates privacy and the dignity of considerations and events of life.
Several countries have opposed it and refer to it as an offence on their human and civil rights. Along with other biological concerns voiced by scientists, R.N.M. remains a controversial technology, which is being used in many countries for security maintenance and surveillance.
Source: http://csglobe.com/remote-neural-monitoring-how-they-spy-on-your-thoughts/
THE TRUTH ABOUT SECRET WEAPONS AND THE INVOLUNTARY TESTING OF THOSE WEAPONS ON CIVILIANS. THE PEOPLE TARGETED INCLUDE MANY WHO CHALLENGE ORGANISED CRIMINAL ACTIVITY WHICH IS CORRUPTLY PROTECTED BY GOVERNMENT / MEDIA INTERESTS.
(Victims can experience hearing voices, mind reading, directed energy attacks and more)

This site contains information relating to advanced satellite surveillance and “harassment” technologies which are made available to covert government agencies and organised crime syndicates.
The secret technologies in question are covered by military/agency secrecy orders, mostly obtained under the US Inventions Secrecy Act, 1951. There are currently over 5,000 hidden devices, many computer – based and satellite facilitated, all with military / criminal applications. A list of known patents is available on the “Surveillance” page after the article on “Social Engineering”. Neurophones, brain scanners and brain wave vocabulary software, directed energy and E-M weapons are amongst these as are technologies to affect the weather, cause earthquakes etc etc. Undemocratically, and to protect powerful criminals from scrutiny,various other Secrecy, National Security and Defamation legislation has been enhanced in recent years.
The US Patriot Act, for example, protects governments and connected criminals from criticism and/or detection and prosecution. Under this act anyone whistleblowing or fighting the system on a major concern is arbitrarily deemed to be unpatriotic (when it’s the criminals they criticise who betray us). They can then be listed (by a senior politician or at the request, through them, of a connected criminal) as a security risk and harassed covertly; using secret technologies. In fact a Dep’t Of Defense Directive, Directive 5240 1-R, 1994, gives open permission for those under surveillance to be used for remote experimentation. It’s no coincidence that this particularly undemocratic and evil move was followed in 1996 by a significant increase in the number of satellites deployed for the purpose of civilian surveillance and harassment. Over 20,000 satellites currently target and silence countless people worldwide (est. 500,000 plus) as a result of such bad laws. The victims are not openly confronted as that would remove any feigned excuses and leave the perpetrators open to all manner of accusation. Instead the methods used are covert; employing high tech’ to remotely torment and deceive victims without leaving evidence. Often targets are tricked into believing they are having psychic, medical, psychiatric, religious or even alien experiences (which they are not). This leaves them discredited as they vainly seek help from ignorant or complicit authorities (police, MPs, doctors, media etc). This leaves them neutralised and possibly even silenced on the issue they originally raised. This, along with various research aspects, is the purpose of the exercise.
The situation is getting worse not better with more and more secretive, undemocratic legislation being sneaked past the unwary public all the time. State treachery and terrorism are behind it yet it is all hidden under the guise of “the war on terror”. For example, the US gov’t just passed the National Defense Authorisation Act, 2012, giving the President (and others) the power to target and silence anyone questioning State corruption. When this is done openly in other countries the US is the first to condemn such evil yet when they are guilty of the same they do it in secret and no-one dares to criticise lest they join the ranks of those they persecute. So much for gov’t of the people, for the people and by the people. The criminals who do such things abuse their authority, betray our trust and secretly mock the democratic ideals they publicly support. They don’t serve us, they simply help themselves and their criminal associates. By using stealth they can feign ignorance and hide their true nature from most.
Eg. In the USA over 300,000 NSL’s (National Security Letters) have already been issued. These allow the agency targeting of innocent civilians whose objections to corruption / crime in high places have been deliberately skewed or misinterpreted as a threat to powerful people. Once placed in a program people can be abused and experimented on, from a distance (using satellites / high tech’). This effectively silences and discredits them while providing agency researchers with guinea pigs for experiments in control, brain function, dreams, health, robotics and much more. Post 9/11, $750 billion per year has been spent on satellite weapons used for human experimentation / targeting. Most of this has found it’s way from gov’t coffers to about 80 defense contractors who are also culpable for the crimes against humanity that are addressed on this site.
There is a circular / Catch 22 type problem in that governments use “classified” covers to hide criminal activity (esp. if it is an unconstitutional act) but targets can’t prove any of that BECAUSE it has been classified…. Eg. NSA Whistleblower William Binney in an interview (seewww.youtube.com/watch?v=TuET0kpHoyM) points out that Executive Order 13526 section 1.7 (covering classified status allocation) specifically says that **”You cannot classify information merely to cover up a crime”**. Even if devices or procedures are classified this also applies to them and information on them when they are being used for criminal purposes. So, in theory, by misusing devices, abusing authority and so on the administration not only commits crimes but should open up the information relating to that for public scrutiny…(Government of, by and for the people). Now Presidents Obama and Bush both signed this executive order 13526 so if any of these hidden crimes was to be presented to the US Supreme Court then any current US leader could be impeached as having breached their oath of office…which includes upholding the constitution. The ECHELON spying system, neurophone harassment, remote neural monitoring, the use of directed energy weapons and more are all clearly crimes against the people and humanity in general and so by classifying the devices the government and it’s leaders are breaching the constitution as well. As with any crime the break in the loop between the acts, investigation, trial and incarceration is the lack of proof. “Classifying” information and calling it a matter of National Security negates the need for the criminals involved to even create excuses for their conduct. The ability of government to classify crime is what must be fought.
Also, the US military is supposed to be prohibited by law from targeting US citizens with PSYOPS within US borders under Executive Order S-1233, DOD directive S-3321.1 and National Security Directive 130. Of course there’s no-one to police that especially since Psyops, by their very nature, are difficult to prove. This is particularly so where the secret weapons discussed on this web site are employed. Also nothing stops agencies, US or allied, from doing that dirty work and hiding it under the National Security carpet. Nonetheless, public discussion of these Psyops crimes is beginning ..eg see Dr Keith Ablow, psychiatrist of Fox News. [ www.foxnews.com/opinion/2013/06/03/is-obama-waging-war-on-americans/ ]
Also, previously The International Commitee of the Red Cross (ICRC) raised the issue of psychotronic weapons; firstly in 1994, then the 2002 Geneva Forum and then the 2009 5th Symposium on non-lethal weapons. The EUROPEAN PARLIAMENT passed a “Resolution on the Environment, Security and Foreign Policy” – A4-0005/99, January 28th, 1999 which called for “An international convention introducing a global ban on ALL development and deployment of weapons which might enable any form of manipulation of human beings”…”It is our conviction that this ban can not be implemented without the global pressure of the informed general public on governments. Our major objective is to get across to the general public the real threat which these weapons represent for human rights and democracy and to apply pressure on the governments and the parliaments around the world to enact legislation which would prohibit the use of these devices to both government AND private organisations as well as individuals”. (Plenary sessions / European Parliament, 1999). ]
Through this site the author seeks to provide a community service; to inform the general public and encourage forthright but peaceful protest against the corporate/military/government crimes outlined herein.
I should also add that whilst the topic of violence (as a sad reality) was addressed in my fictional novel, “In the year 2252″, at no stage and in no way was it my intention to encourage violent responses to the real life criminal conduct of corrupt members of corporate/government/military organisations. Passive resistance to oppression is the only acceptable method … but resist we must.
Contact: Paul Baird
Email: [email protected] (please put ‘surveillance’ in the subject line)
The Government Is Spying On Us Through Our Computers, Phones, Cars, Buses, Streetlights, At Airports And On The Street, Via Mobile Scanners And Drones, Through Our Smart Meters, And In Many Other Ways
Take a Peek at How Widespread Spying Has Become
Even now – after all of the revelations by Edward Snowden and other whistleblowers – spying apologists say that the reports are “exaggerated” or “overblown”, and that the government only spies on potential bad guys.
In reality, the government is spying on everyone’s digital and old-fashioned communications.
For example, the government is photographing the outside information on every piece of snail mail.
The government is spying on you through your phone … and may even remotely turn on your camera and microphone when your phone is off.
As one example, the NSA has inserted its code into Android’s operating system … bugging three-quarters of the world’s smartphones. Google – or the NSA – can remotely turn on your phone’s camera and recorder at any time.
Moreover, Google knows just about every WiFi password in the world … and so the NSA does as well, since it spies so widely on Google.
But it’s not just the Android. In reality, the NSA can spy on just about everyone’s smart phone.
Cell towers track where your phone is at any moment, and the major cell carriers, including Verizon and AT&T, responded to at least 1.3 million law enforcement requests for cell phone locations and other data in 2011. (And – given that your smartphone routinely sends your location information back to Apple or Google – it would be child’s play for the government to track your location that way.) Your iPhone, orother brand of smartphone is spying on virtually everything you do (ProPublica notes: “That’s No Phone. That’s My Tracker“). Remember, that might be happening even when your phone is turned off.
The government might be spying on you through your computer’s webcam or microphone. The government might also be spying on you through the “smart meter” on your own home.
NSA also sometimes uses “man-in-the-middle” tactics, to pretend that it is Google or other popular websites to grab your information.
The FBI wants a backdoor to all software. But leading European computer publication Heise said in 1999 that the NSA had already built a backdoor into all Windows software.
Microsoft has long worked hand-in-hand with the NSA and FBI so that encryption doesn’t block the government’s ability to spy on users of Skype, Outlook, Hotmail and other Microsoft services.
And Microsoft informs intelligence agencies of with information about bugs in its popular softwarebefore it publicly releases a fix, so that information can be used by the government to access computers. (Software vulnerabilities are also sold to the highest bidder.)
A top expert in the ‘microprocessors’ or ‘chips’ inside every computer – having helped start two semiconductor companies and a supercomputer firm – also says:
He would be “surprised” if the US National Security Agency was not embedding “back doors” inside chips produced by Intel and AMD, two of the world’s largest semiconductor firms, giving them the possibility to access and control machines.
***
[The expert] said when he learned the NSA had secured “pre-encryption stage” access to Microsoft’s email products via the PRISM leaks, he recognised that “pretty much all our computers have a way for the NSA to get inside their hardware” before a user can even think about applying encryption or other defensive measures.
Leading security experts say that the NSA might have put a backdoor in all encryption standards years ago. … meaning that the NSA could easily hack into all encrypted communications. And the NSA hacks into encrypted “VPN” connections.
It’s gotten so bad that some of the largest encryption companies are warning that their encryption tools are compromised.
“Black boxes” are currently installed in between 90% and 96% of all new cars. And starting in 2014, all new cars will include black boxes that can track your location.
License plate readers mounted on police cars allow police to gather millions of records on drivers … including photos of them in their cars.
If you have a microphone in your car, that might also open you up to snoopers. As CNET points out:
Surreptitious activation of built-in microphones by the FBI has been done before. A 2003 lawsuit revealed that the FBI was able to surreptitiously turn on the built-in microphones in automotive systems like General Motors’ OnStar to snoop on passengers’ conversations.
When FBI agents remotely activated the system and were listening in, passengers in the vehicle could not tell that their conversations were being monitored.
A security expert and former NSA software developer says that hackers can access private surveillance cameras. Given that the NSA apparently already monitors public cameras using facial recognition software (and see this), and that the FBI is building a system which will track “public and privatesurveillance cameras around the country”, we can assume that government agencies might already be hacking into private surveillance cameras.
The CIA wants to spy on you through your dishwasher and other “smart” appliances. As Slate notes:
Watch out: the CIA may soon be spying on you—through your beloved, intelligent household appliances, according to Wired.
In early March, at a meeting for the CIA’s venture capital firm In-Q-Tel, CIA Director David Petraeus reportedly noted that “smart appliances” connected to the Internet could someday be used by the CIA to track individuals. If your grocery-list-generating refrigerator knows when you’re home, the CIA could, too, by using geo-location data from your wired appliances, according to SmartPlanet.
“The current ‘Internet of PCs’ will move, of course, toward an ‘Internet of Things’—of devices of all types—50 to 100 billion of which will be connected to the Internet by 2020,”Petraeus said in his speech. He continued:
Items of interest will be located, identified, monitored, and remotely controlled through technologies such as radio-frequency identification, sensor networks, tiny embedded servers, and energy harvesters—all connected to the next-generation Internet using abundant, low cost, and high-power computing—the latter now going to cloud computing, in many areas greater and greater supercomputing, and, ultimately, heading to quantum computing.
***
ITworld’s Kevin Fogarty thinks that J. Edgar Hoover, were he still with us, would “die of jealousy” upon hearing about the tools soon to be at Petraeus’ disposal.
And they’re probably bluffing and exaggerating, but the Department of Homeland Security claims they will soon be able to know your adrenaline level, what you ate for breakfast and what you’re thinking …from 164 feet away. (In addition, people will probably soon be swallowing tracking devices for medical purposes)
The government is allegedly scanning prisoners’ brains without their consent at Guantanamo. In the near future, brain scanners may be able to literally read our thoughts (and see this).
The government is currently testing systems for use in public spaces which can screen for “pre-crime”. As Nature reports:
Like a lie detector, FAST measures a variety of physiological indicators, ranging from heart rate to the steadiness of a person’s gaze, to judge a subject’s state of mind. But there are major differences from the polygraph. FAST relies on non-contact sensors, so it can measure indicators as someone walks through a corridor at an airport, and it does not depend on active questioning of the subject.
CBS News points out:
FAST is designed to track and monitor, among other inputs, body movements, voice pitch changes, prosody changes (alterations in the rhythm and intonation of speech), eye movements, body heat changes, and breathing patterns. Occupation and age are also considered. A government source told CNET that blink rate and pupil variation are measured too.
A field test of FAST has been conducted in at least one undisclosed location in the northeast. “It is not an airport, but it is a large venue that is a suitable substitute for an operational setting,” DHS spokesman John Verrico told Nature.com in May.
Although DHS has publicly suggested that FAST could be used at airport checkpoints–the Transportation Security Administration is part of the department, after all–the government appears to have grander ambitions. One internal DHS document (PDF) also obtained by EPIC through the Freedom of Information Act says a mobile version of FAST “could be used at security checkpoints such as border crossings or at large public events such as sporting events or conventions.”
The risk of false positives is very real. As Computer World notes:
Tom Ormerod, a psychologist in the Investigative Expertise Unit at Lancaster University, UK, told Nature, “Even having an iris scan or fingerprint read at immigration is enough to raise the heart rate of most legitimate travelers.” Other critics have been concerned about “false positives.” For example, some travelers might have some of the physical responses that are supposedly signs of mal-intent if they were about to be groped by TSA agents in airport security.
Various “pre-crime” sensing devices have already been deployed in public spaces in the U.S.
The government has also worked on artificial intelligence for “pre-crime” detection on the Web. And given that programs which can figure out your emotions are being developed using your webcam, every change in facial expression could be tracked.
According to the NSA’s former director of global digital data – William Binney – the NSA’s new data storage center in Utah will have so much storage capacity that:
“They would have plenty of space … to store at least something on the order of 100 years worth of the worldwide communications, phones and emails and stuff like that,” Binney asserts, “and then have plenty of space left over to do any kind of parallel processing to try to break codes.”
***
[But the NSA isn’t stopping there.] Despite its capacity, the Utah center does not satisfy NSA’s data demands. Last month, the agency broke ground on its next data farm at its headquarters at Ft. Meade, Md. But that facility will be only two-thirds the size of the mega-complex in Utah.
The NSA is building next-generation quantum computers to process all of the data.
NBC News reports:
NBC News has learned that under the post-9/11 Patriot Act, the government has been collecting records on every phone call made in the U.S.
This includes metadata … which can tell the government a lot about you. And it also includes content.
The documents leaked by Edward Snowden to Glenn Greenwald show:
But what we’re really talking about here is a localized system that prevents any form of electronic communication from taking place without its being stored and monitored by the National Security Agency.
It doesn’t mean that they’re listening to every call, it means they’re storing every call and have the capability to listen to them at any time, and it does mean that they’re collecting millions upon millions upon millions of our phone and email records.
In addition, a government expert told the Washington Post that the government “quite literally can watch your ideas form as you type.” (And see this.) A top NSA executive confirmed to Washington’s Blog that the NSA is intercepting and storing virtually all digital communications on the Internet.
McClatchy notes:
FBI Director Robert Mueller told a Senate committee on March 30, 2011, that “technological improvements” now enable the bureau “to pull together past emails and future ones as they come in so that it does not require an individualized search.”
The administration is building a facility in a valley south of Salt Lake City that will have the capacity to store massive amounts of records – a facility that former agency whistleblowers say has no logical purpose if it’s not going to be a vault holding years of phone and Internet data.
***
Thomas Drake, a former NSA senior executive who challenged the data collection for several years, said the agency’s intent seems obvious.
“One hundred million phone records?” he asked in an interview. “Why would they want that each and every day? Of course they’re storing it.”
***
Lending credence to his worries, The Guardian’s latest report quoted a document in which Alexander purportedly remarked during a 2008 visit to an NSA intercept station in Britain: “Why can’t we collect all the signals all the time?”
***
One former U.S. security consultant, who spoke on condition of anonymity to protect his connections to government agencies, told McClatchy he has seen agency-installed switches across the country that draw data from the cables.
“Do I know they copied it? Yes,” said the consultant. “Do I know if they kept it? No.”
NSA whistleblower Russel Tice – a key source in the 2005 New York Times report that blew the lid off the Bush administration’s use of warrantless wiretapping – says that the content and metadata of alldigital communications are being tapped by the NSA.
The NSA not only accesses data directly from the largest internet companies, it also sucks up huge amounts of data straight from undersea cables providing telephone and Internet service to the United States.
After all, the government has secretly interpreted the Patriot Act so that “everything” is deemed relevant … so the government can spy on everyone.
The NSA isn’t the only agency which is conducting massive spying.
The Wall Street Journal notes:
The rules now allow the little-known National Counterterrorism Center to … copy entire government databases—flight records, casino-employee lists, the names of Americans hosting foreign-exchange students and many others. The agency has new authority to keep data about innocent U.S. citizens for up to five years, and to analyze it for suspicious patterns of behavior. Previously, both were prohibited. Data about Americans “reasonably believed to constitute terrorism information” may be permanently retained.
The changes also allow databases of U.S. civilian information to be given to foreign governments for analysis of their own. In effect, U.S. and foreign governments would be using the information to look for clues that people might commit future crimes.
“It’s breathtaking” in its scope, said a former senior administration official familiar with the White House debate.
Reason notes:
Gazillions. That’s the number of times the federal government has spied on Americans since 9/11 through the use of drones, legal search warrants, illegal search warrants, federal agent-written search warrants and just plain government spying. This is according to Sen. Rand Paul, R-Ky., who, when he asked the government to tell him what it was doing to violate our privacy, was given a classified briefing. The senator — one of just a few in the U.S. Senate who believes that the Constitution means what it says — was required by federal law to agree not to reveal what spies and bureaucrats told him during the briefing.
Even if the US government weren’t recording all of that data, England’s GCHQ spy agency is … and issharing it with the NSA.
Germany, Australia, Canada and New Zealand are also recording and sharing massive amounts of information with the NSA.
Private contractors can also view all of your data … and the government isn’t keeping track of which contractors see your data and which don’t. And because background checks regarding some contractors are falsified, it is hard to know the types of people that might have your information.
And top NSA and FBI experts say that the government can retroactively search all of the collected information on someone since 9/11 if they suspect someone of wrongdoing … or want to frame him.
The American government is in fact collecting and storing virtually every phone call, purchases, email, text message, internet searches, social media communications, health information, employment history, travel and student records, and virtually all other information of every American.
The Wall Street Journal reported that the NSA spies on Americans’ credit card transactions. Senators Wyden and Udall – both on the Senate Intelligence Committee, with access to all of the top-secret information about the government’s spying programs – write:
Section 215 of the Patriot Act can be used to collect any type of records whatsoever … including information on credit card purchases, medical records, library records, firearm sales records, financial information and a range of other sensitive subjects.
Many other government agencies track your credit card purchases as well. In fact, all U.S. intelligence agencies – including the CIA and NSA – are going to spy on Americans’ finances.
The IRS will be spying on Americans’ shopping records, travel, social interactions, health records and files from other government investigators.
The Consumer Financial Protection Board will also spy on the finances of millions of Americans.
As Washington Monthly noted in 2004, Congress chopped off the head of the Total Information Awareness program … but the program returned as a many-headed hydra:
A program can survive even when the media, the public, and most of Congress wants it killed. It turns out that, while the language in the bill shutting down TIA was clear, a new line had been inserted during conference—no one knew by whom—allowing “certain processing, analysis, and collaboration tools” to continue.
….Thanks to the Central Intelligence Agency and the National Security Agency, which had lobbied for the provision, TIA didn’t die—it metastasized. As the AP reported in February [of 2004], the new language simply outsourced many TIA programs to other intelligence offices and buried them in the so-called “black budget.” What’s more, today, several agencies are pursuing data mining projects independent of TIA, including the Department of Homeland Security, the Justice Department, the CIA, the Transportation Security Administration, and NASA….Even with TIA ostensibly shut down, many of the private contractors who worked on the program can continue their research with few controls.
The government is flying drones over the American homeland to spy on us. Indeed, the head of the FBI told Congress that drones are used for domestic surveillance … and that there are no rules in placegoverning spying on Americans with drones.
Senator Rand Paul correctly notes:
The domestic use of drones to spy on Americans clearly violates the Fourth Amendment and limits our rights to personal privacy.
Emptywheel notes in a post entitled “The OTHER Assault on the Fourth Amendment in the NDAA? Drones at Your Airport?”:
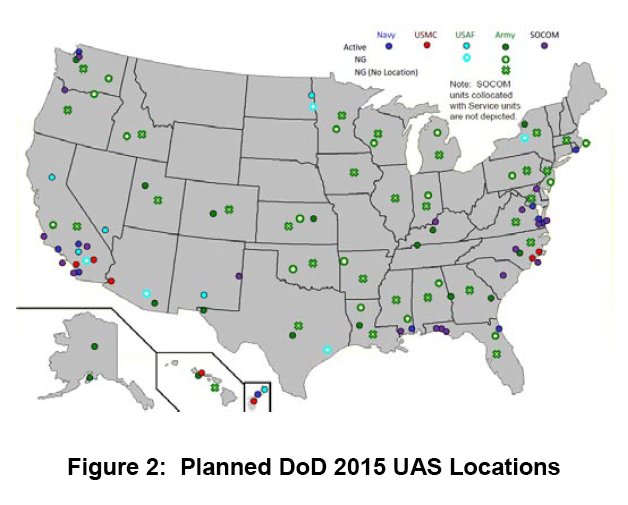
***As the map above makes clear–taken from this 2010 report–DOD [the Department of Defense] plans to have drones all over the country by 2015.
Many police departments are also using drones to spy on us. As the Hill reported:
At least 13 state and local police agencies around the country have used drones in the field or in training, according to the Association for Unmanned Vehicle Systems International, an industry trade group. The Federal Aviation Administration has predicted that by the end of the decade, 30,000 commercial and government drones could be flying over U.S. skies.
***
“Drones should only be used if subject to a powerful framework that regulates their use in order to avoid abuse and invasions of privacy,” Chris Calabrese, a legislative counsel for the American Civil Liberties Union, said during a congressional forum in Texas last month.
He argued police should only fly drones over private property if they have a warrant, information collected with drones should be promptly destroyed when it’s no longer needed and domestic drones should not carry any weapons.
He argued that drones pose a more serious threat to privacy than helicopters because they are cheaper to use and can hover in the sky for longer periods of time.
A congressional report earlier this year predicted that drones could soon be equipped with technologies to identify faces or track people based on their height, age, gender and skin color.
The military is paying for the development of drones with facial recognition software which “remember” people’s faces … and read “malintent”.
Moreover, Wired reports:
Transit authorities in cities across the country are quietly installing microphone-enabled surveillance systems on public buses that would give them the ability to record and store private conversations….
The systems are being installed in San Francisco, Baltimore, and other cities with funding from the Department of Homeland Security in some cases ….
The IP audio-video systems can be accessed remotely via a built-in web server (.pdf), and can be combined with GPS data to track the movement of buses and passengers throughout the city.
***
The systems use cables or WiFi to pair audio conversations with camera images in order to produce synchronous recordings. Audio and video can be monitored in real-time, but are also stored onboard in blackbox-like devices, generally for 30 days, for later retrieval. Four to six cameras with mics are generally installed throughout a bus, including one near the driver and one on the exterior of the bus.
***
Privacy and security expert Ashkan Soltani told the Daily that the audio could easily be coupled with facial recognition systems or audio recognition technology to identify passengers caught on the recordings.
Street lights that can spy installed in some American cities
America welcomes a new brand of smart street lightning systems: energy-efficient, long-lasting, complete with LED screens to show ads. They can also spy on citizens in a way George Orwell would not have imagined in his worst nightmare.
With a price tag of $3,000+ apiece, according to an ABC report, the street lights are now being rolled out in Detroit, Chicago and Pittsburgh, and may soon mushroom all across the country.
Part of the Intellistreets systems made by the company Illuminating Concepts, they havea number of “homeland security applications” attached.
Each has a microprocessor “essentially similar to an iPhone,” capable ofwireless communication. Each can capture images and count people for the police through a digital camera, record conversations of passers-by and even give voice commands thanks to a built-in speaker.
Ron Harwood, president and founder of Illuminating Concepts, says he eyed the creation of such a system after the 9/11 terrorist attacks and the Hurricane Katrina disaster. He is“working with Homeland Security” to deliver his dream of making people “more informed and safer.”
The TSA has moved way past airports, trains and sports stadiums, and is deploying mobile scanners to spy on people all over the place. This means that traveling within the United States is no longer a private affair.
You might also have seen the news this week that the Department of Homeland Security is going tocontinue to allow searches of laptops and phones based upon “hunches”.
What’s that about?
The ACLU published a map in 2006 showing that nearly two-thirds of the American public – 197.4 million people – live within a “constitution-free zone” within 100 miles of land and coastal borders:
The ACLU explained:
- Normally under the Fourth Amendment of the U.S. Constitution, the American people are not generally subject to random and arbitrary stops and searches.
- The border, however, has always been an exception. There, the longstanding view is that the normal rules do not apply. For example the authorities do not need a warrant or probable cause to conduct a “routine search.”
- But what is “the border”? According to the government, it is a 100-mile wide strip that wraps around the “external boundary” of the United States.
- As a result of this claimed authority, individuals who are far away from the border, American citizens traveling from one place in America to another, are being stopped and harassed in ways that our Constitution does not permit.
- Border Patrol has been setting up checkpoints inland — on highways in states such as California, Texas and Arizona, and at ferry terminals in Washington State. Typically, the agents ask drivers and passengers about their citizenship. Unfortunately, our courts so far have permitted these kinds of checkpoints – legally speaking, they are “administrative” stops that are permitted only for the specific purpose of protecting the nation’s borders. They cannot become general drug-search or other law enforcement efforts.
- However, these stops by Border Patrol agents are not remaining confined to that border security purpose. On the roads of California and elsewhere in the nation – places far removed from the actual border – agents are stopping, interrogating, and searching Americans on an everyday basis with absolutely no suspicion of wrongdoing.
- The bottom line is that the extraordinary authorities that the government possesses at the border are spilling into regular American streets.
Computer World reports:
Border agents don’t need probable cause and they don’t need a stinking warrant since they don’t need to prove any reasonable suspicion first. Nor, sadly, do two out of three people have First Amendment protection; it is as if DHS has voided those Constitutional amendments and protections they provide to nearly 200 million Americans.
***Don’t be silly by thinking this means only if you are physically trying to cross the international border. As we saw when discussing the DEA using license plate readers and data-mining to track Americans movements, the U.S. “border” stretches out 100 miles beyond the true border. Godfather Politics added:
But wait, it gets even better! If you live anywhere in Connecticut, Delaware, Florida, Hawaii, Maine, Massachusetts, Michigan, New Hampshire, New Jersey or Rhode Island, DHS says the search zones encompass the entire state.
Immigrations and Customs Enforcement (ICE) and Customs and Border Protection (CBP) have a “longstanding constitutional and statutory authority permitting suspicionless and warrantless searches of merchandise at the border and its functional equivalent.” This applies to electronic devices, according to the recent CLCR “Border Searches of Electronic Devices” executive summary [PDF]:
Fourth Amendment
The overall authority to conduct border searches without suspicion or warrant is clear and longstanding, and courts have not treated searches of electronic devices any differently than searches of other objects. We conclude that CBP’s and ICE’s current border search policies comply with the Fourth Amendment. We also conclude that imposing a requirement that officers have reasonable suspicion in order to conduct a border search of an electronic device would be operationally harmful without concomitant civil rights/civil liberties benefits. However, we do think that recording more information about why searches are performed would help managers and leadership supervise the use of border search authority, and this is what we recommended; CBP has agreed and has implemented this change beginning in FY2012.***
The ACLU said, Wait one darn minute! Hello, what happened to the Constitution? Where is the rest of CLCR report on the “policy of combing through and sometimes confiscating travelers’ laptops, cell phones, and other electronic devices—even when there is no suspicion of wrongdoing?” DHS maintains it is not violating our constitutional rights, so the ACLU said:
If it’s true that our rights are safe and that DHS is doing all the things it needs to do to safeguard them, then why won’t it show us the results of its assessment? And why would it be legitimate to keep a report about the impact of a policy on the public’s rights hidden from the very public being affected?
***As Christian Post wrote, “Your constitutional rights have been repealed in ten states. No, this isn’t a joke. It is not exaggeration or hyperbole. If you are in ten states in the United States, your some of your rights guaranteed by the Bill of Rights have been made null and void.”
The ACLU filed a Freedom of Information Act request for the entire DHS report about suspicionless and warrantless “border” searches of electronic devices. ACLU attorney Catherine Crump said “We hope to establish that the Department of Homeland Security can’t simply assert that its practices are legitimate without showing us the evidence, and to make it clear that the government’s own analyses of how our fundamental rights apply to new technologies should be openly accessible to the public for review and debate.”
Meanwhile, the EFF has tips to protect yourself and your devices against border searches. If you think you know all about it, then you might try testing your knowledge with a defending privacy at the U.S. border quiz.
Wired pointed out in 2008 that the courts have routinely upheld such constitution-free zones:
Federal agents at the border do not need any reason to search through travelers’ laptops, cell phones or digital cameras for evidence of crimes, a federal appeals court ruled Monday, extending the government’s power to look through belongings like suitcases at the border to electronics.
***
The 9th U.S. Circuit Court of Appeals sided with the government, finding that the so-called border exception to the Fourth Amendment’s prohibition on unreasonable searches applied not just to suitcases and papers, but also to electronics.
***
Travelers should be aware that anything on their mobile devices can be searched by government agents, who may also seize the devices and keep them for weeks or months. When in doubt, think about whether online storage or encryption might be tools you should use to prevent the feds from rummaging through your journal, your company’s confidential business plans or naked pictures of you and your-of-age partner in adult fun.
International airports are treated as “borders”, exempt for Fourth Amendment protections. As such, 145airports should be added to the map above.
Do you still believe that the government is only spying on bad guys in “targeted” searches?
V2K (Voice to Skull) Torture
Imagine a weapon that creates sound that only you can hear. Science fiction? No, this is one area that has a very solid basis in reality. US Air Force has experimented with microwaves that create sounds in people’s head (which they’ve called a possible psychological warfare tool), and American Technologies can “beam” sounds to specific targets with their patented HyperSound Now the Defense Advanced Research Projects Agency is jumping on the bandwagon with their new “Sonic Projector” program.
For about 30 years, anti-personnel directed energy devices have been feasible that cause targeted individuals to hear voices (and other sounds) that other people near the targeted individuals cannot hear. The voices can be loud enough to be consciously audible, or so quiet that they have whatever effect they have subliminally. V2K weapons can inflict their effects upon their victims through solid brick and stone walls.
The United States of America’s Army’s “Military Thesaurus” defines “Voice to skull” (V2K) devices as follows:
“Voice to skull device is a Non-lethal weapon which includes (1) a neuro-electromagnetic device that uses microwave transmission of sound into the skull of persons or animals by way of pulse-modulated microwave radiation; and (2) a silent sound device which can transmit sound into the skull of persons or animals. NOTE: the sound modulation may be voice or audio subliminal messages. . Acronym: V2K”.
V2K weapons fall within a class of weapons, those that “might enable any form of manipulation of human beings”, of which the European Parliament called for a worldwide ban, in 1999. For reasons of so-called “national security”, questions to the UK government remain unanswered, about the availability of such weapons to the public and private sectors nowadays..
The device – dubbed MEDUSA (Mob Excess Deterrent Using Silent Audio) – exploits the microwave audio effect, in which short microwave pulses rapidly heat tissue, causing a shockwave inside the skull that can be detected by the ears. A series of pulses can be transmitted to produce recognizable sounds.(Please note that, V2K Torture can be done with Neurophones also.)
These kinds of non-lethal weapons are often used in Mind Control, to produce a feeling of “gang-raping” a person’s brain …..Some victim tries to describe his personal experience with Mind Control in this way …
“Like a nail being slowly hammered the head gets beat. Beaten and beaten till you can’t make it. Your brain is being destroyed, bit by bit. Noise in your ears seems to come from contact with microwaves. Implants that respond to microwaves.The RNA structure of your brain is being changed by microwaves, slowly but surely. The clever hypnotist has a hold of you like a wash rag. he’ll ring you out till your used up! WELCOME TO HELL ..”
Brain damage risk
James Lin of the Electrical and Computer Engineering Department at the University of Illinois in Chicago says that MEDUSA is feasible in principle.
He has carried out his own work on the technique, and was even approached by the music industry about using microwave audio to enhance sound systems, he told New Scientist.
“But is it going to be possible at the power levels necessary?” he asks. Previous microwave audio tests involved very “quiet” sounds that were hard to hear, a high-power system would mean much more powerful – and potentially hazardous – shockwaves.
“I would worry about what other health effects it is having,” says Lin. “You might see neural damage.”
My Own Experience with this kind of torture
This is the most sophisticated form of “psychological murder” one can think of, and is used to threaten me criminally and to destroy my brain and nerves intentionally & completely to a vegetative state..To begin with, this was draconian violation of privacy, life and liberty,& in fact, in a nutshell, in one fell swoop, it criminally violates all human rights that a human being is entitled to.
Even though it sounds weird to the common people, it’s a fact that, I get tortured the most by faceless voices inside my head (and I’m not a psychiatric patient), that continuously negates & manipulate my thought process and weakens and exhausts my brain and nerves through remotely operated technologies as mentioned above. My mind is always a battlefield in here, and my brain just “gasps” every second to take a breath and it seems like that these are just suffocating my brain to “death”. I remain helplessly mentally handicapped in this condition. The perpetrators do it intentionally and increase the severity when it counts the most. They don’t even let me sleep at night. This pushes me towards acute depression, mental retardation and insanity almost. This is so intolerable that someone who has not gone through it can’t even imagine. This continuous torture on my brain & nerves may result in permanent insanity, brain embolism, cerebral hemorrhage etc.
Other Victim’s Experiences: –
“Electromagnetic radiation communication of sound has been used against me 24/7 for three years and four months starting in February 2001 no matter where I am located. A key person involved is well known to me, so there are no mystery voices here.
It’s interesting to note that this is pulsed which drops part of the frequency used down to the level of brain wave frequency which can be as a low as 10 Hertz.
The new UK TETRA system for police communications pulses at about 17 Hertz and is generating fears of what this will do to the brains of the officers using these mobile phones. Pulsing the high frequency microwave transmission allows multiple phone calls to be sent like packets on the Internet.
The basic high frequency drives the electromagnetic radiation deep into the brain while the pulsing of that transmission at the incredibly low rate matches the brain wave frequency which, I suspect, is what results in the ability to hear.
This could prove to be quite harmful and lethal in many instances. It’s not exactly a “Non Lethal Weapon” and is an instrument of torture interrogation with lethal consequences from its usage. It is not being used for just scaring birds away.
Another Victim’s Experience
Inhibition of thought: drowsiness, inability to recall words, or think incoherently are the most noticeable effects of thought inhibition. Perps block thoughts from surfacing by yanking me every time I show a tendency to “think.” It’s usually when the feeling you get that you know you’re about to think out something. What happens when they do that to every thought that surface is that my brain can’t focus and process anything that my senses receive. I can still try to process information, but then they will yank harder to distract me or bending my feet continuously when I still sit there and try to think. Apparently when the brain is not active, it starts to feel drownsy. They can only block the ability to recall word IF I’m not familiar with the word. I learn language much later so to remember the meaning of some of the word, sometimes I had to recall the words use in some situation. Apparently recalling some of the words using over and over again is much easier than some other, and distracting someone from remembering something that they already had trouble remember is easier than some other word that the brain is more familiar with. Zoning out helps the brain to recall events happened, therefore, sometimes they blink my eyes continuously to snap my brain into that state where my brain is restricted to the point where I can’t think of everything else or recalling anything or making connection between the things I see with my eyes. Usually the brain can make an association when it sees a stimuli with something that is familiar with something it “sees” before (an example of this is that people usually claim :”you reminds me of someone I know..”). For every association, reacalling that the brain makes, they deliver pain (sharp pain) enough to make me sitting still not thinking up of anything for hours and hours. Apparently when you don’t know, when your subject will passively recall facts to make a connection and tell the pattern, the best thing to do is to inhibit everything. Delivering pain after every thought however, may make the subject sitting still and blank. Somehow I still manage to write some things up here which implies distraction only work at a certain levels, it may weaken the signal but it does not quench it completely.
Surveillance: A Most Unreasonable Search and Seizure
Satellite surveillance is a most unreasonable search and seizure by totally invading the privacy of an individual as it “steals” everything it observes including all personal and private activities, documentation and anything which might be available in the private life of that individual. Furthermore, the surveillance activity can be used to shutdown and stop legitimate free exercise of rights and responsibilities by an individual by interfering with the very life and activity processes it purports to observe.
The worst aspect of surveillance activity is its perversion by an abuse of its power wherein it is used to create the very outcome which it purports to be objectively observing.”














I am a synical, suspicious old lady – know this of me.
After much deliberation I have come to believe that
* Edward Snowden & * Julian Assange – are establishment puppets.
exerpts from – Microwave Hearing – Youtube
“Microwaves & other radio frequencies are known to effect the human body, but could they be responsible for the voices in peoples heads.”
And Therefore we know that – THE – mental illness SCHIZOPHRENIA – is people with enhanced hearing, hearing microwave & other radio frequency sounds….therefore these people are known to the establishment as BYSTANDER EAVESDROPPERS : unintentionally hearing top secret information.
* A while ago I wrote in comment to schizophrenia & the voices – that the sufferes of schizophrenia are actually hear energy – that is then interpreted by the brain, which is what a brain does for a living.
* I am not sure that a human ear can hear without the brain to process & interpret / decipher & put into context what is heard.
NOW HERE IS THE PROBLEM FOR ME –
The brain must interpret – it is each persons individual brain capacity / ability / compatibility etc., that ultimately decides what the message is – what message is being transmitted & not what message, the establishment ghoules might send / transmit – and want the receiver to hear / pick up.
Music – Puccini does it to me – I cannot listen to Madam Butterfly without crying – years ago, my mother walked in on me watching a performance of Madam Butterfly on the IDIOT BOX, as I wept into a towel, one afternoon – she looked at the TV, she looked at the emotional mess that I was & realized that I was insane.
Depending on each persons individuals makeup – sound has an individual effect on each of us.
AND THEREFORE
GO FIND THE FEW THAT WILL PICK UP AND HEAR THE MESSAGE THAT YOU ARE SENDING AS YOU WANT IT TO BE UNDERSTOOD – MATE
With the millions of individuals on planet earth I reckon you might find a few.
It is The Great Wizz beating on his preverbially hairy chest again.
Someone is drinking funny tea still & again.
I would probably agree with you on Snowden & Assange as the public need these types of Robin Hood heroes to look up to. I guess it makes people feel more safer to know that these folks are out there, fighting & exposing evil. The establishment has a sick need to show us whats being done but not so much in real time so people still do need to take certain information & separate it from what they believe to be false or misleading. The enhanced hearing & SCHIZOPHRENIA side of things is very interesting & iv always wondered, are so called schizo’s really just extremely sensitive to energies. Brian Wilson of the beach boys was druged to his eyeballs but in the film, love & mercy you can see that he was hearing voices & music in his head that he transferred into his music, Petsounds. I think this post has some incredible info & who’s to say the military, for example are not 50 or 100 years ahead in technology & this sort of stuff. If Snowden is supposedly leaking all this frightening info out to the public then it would make perfect sense that the info is old news for the establishment, just like our technology.
I’m a Targeted Individual (TI).
I have caught the audio recording evidence or proof of Remote Neural Monitoring (RNM), Voice to skull (V2K) See here https://www.youtube.com/watch?v=kN4QCVwiUsI&list=PL42RBzMkobFQW9tHMsXGjJ-wHLWK-lv4E
For detailed explanation of methods used for harassment from my personal experience by Remote Neural Monitoring (RNM), Voice to skull (V2K) visit https://remoteneuralmonitoringv2kevidence.blogspot.in/
My Name is Brian Neitzel . I am a victim of RNM (V2K) with 2 Main character Voices. It took a long time to figure out what was going on. I have a Technical background which helped Awaken Me. How does Mankind stop this Holocaust. Any input is very much appreciated. Thank You !
I wabt to sue…!!!
This is happening to me and I’m on the brink of suicide.
Message body
Please note that email below is sent 2, 3 September 2018 to date their is no response from yourself therefore as it’s a matter of urgency your quick response to the email below will be appreciated
20 December 2016
Dear Sir / Madam,
I the undersign I am writing to as aBSc Tellecommunication victim of The London Pentonville Prison Authority V2K Electronic harassment you are on record as Voice to skull media organization and also as an someone who is deeply concerned and trying to raise awareness regarding the seriousness of crimes committed by voice to skull Harassment technology ” as Dr ALLEN BARKER Ph.D at MIND CONTROL – TECHNOLOGY, TECHNIQUES & POLITICS stated “much of the technology is truly amazing and has great potential for positive uses. But unfortunately, in practice, it has been tested on nonconsensual subjects and applied to violate fundamental human rights in almost unthinkable ways.” I would like to therefore state.
I received email below and The London Parliamentry Ombudsman has confirmed that The pentonville prison authority has Voice to skull Technology and will confirm investigation regarding the Pentonville prison authority voice to skull electronic harassment human right abuse therefore the pentonville prison authority DEW Voice to skull electronic harassment against me is increasing therefore I would like to request your help regarding to below email and Jammer
Email Received
please help me im am being murdered by a DEW and i don’t know how to stop it.I am positive this is being done to me by the vancouver police and the rcmp ..Please how can i stop it if there is a way?? Is there a jammer that can stop this deadly weapon or is there anything i can do please call me 604-657-8429 Murray please help save my life
Also I would like to request your help regarding signing the petition against the pentonville prison authority voice to skull electronic harassment against me Which could result in a European Law against Voice to skull electronic harassment Human right Abuse
IN THE HIGH COURT OF JUSTICE
Between:-
Proposed Claimant: Yaya Jawara
And
Proposed Defendant: The H M Prison Service
—————————— —-
PETITION STATEMENT REGARDING LEGAL UNDERTAKEN
—————————— —-
I, ……………………………………….. ………………………………………A Concerned Citizen ,Qualification/Job Title………………………………………………………………… ..Email [email protected]
………………………… ………………………..
Having read the Legal undertaken given to Pentonville Prison London on 10 June 2014 in behalf of Mr Yaya Jawara and having been reliable informed of The Pentonville Prison Authorities [Particularly a Ms Janet Web] Lack of a response regarding the above stated Legal document. I would like to express my deep concern regarding human rights abuses by the Pentonville Prison Authorities [by way of the use of remote voice to skull & other RF/EMF weapons] and I the undersigned would like to kindly request a response to the Legal undertaken document given to The Pentonville Prison Authorities
I believe that the facts stated in this Petition Statement are true.
Print name……………………………………………………………..
Signed ……………………………………………………………..
Dated this day of 2016
Also present and pentonville prison authority voice to skull electronic harassment experience isresult and above email is awakw and target touch Jammer and clean toilet roll and intencintense pain and DEW and The Unothorise Pentonville Prison Authority as target touch you target touch toilet roll and jammer also dew to intense pain sleep the Unothorise Pentonville Prison Authority you wash Jammer and clean toilet roll as beams passed blttom of genital intense irritation hip intense pain left side chest intense pain and head swollen intense pain and lower back intense pain also result and sleep beam were passed across genital until a discharge did occuralso whist whist sweater and address the Unothorise pentonville prison authority state as sweater and address sweater sweter and and trouser and Toiwel whilst sweater also stated is The Unothorise Pentonville Prison Authority is is stocking and voilating you and Ken at pentonvelectronic targeting also electronic stocking and violating you and Ken at Pentonville Prison and SStockfield and Ken Prisonthis is human right abuse what could you and Ken defend as above beam Unothorise Pentonville Prison Authority electronic harassement is presentalso also ken and you see eand Yourgurt the penUnothiruse Pentonville Prison Authority state you see eggand this is stated repeatedly whist shopping and waitrose thereforeyour help is being requested in investigating and publishing note below see link in note
note or letter to publish
Dear Sir / Madam,
The following in addition to my 2 diary[ email contact details below for diary] is my story, I was sentence to pentonville in Jan 2005 whilst there I started to experience voice to skull electronic harassment as set out in my diary i.e names of Prison Officer being stated to me as prison officer A is your fancy and whilst this occur this was followed by intense pain of DEW electronic harassment i.e beams passed across bottom of feet and arms result intense hot also beams passed across lower back, head [swollen, I have pictures of head swollen by beams]and hip result INTENSE PAIN. Also occured beams were passed across genital until a discharge did occur and the names of prison officer harassing me would be repeated by The Pentonville Prison Authorities in London, as a victim of a technology I had not even heard of see http://loveforlife.com.au/ content/13/05/23/torture- report-dr-les-dove-cph- updated-april-2013 and as my attacker were the Prison Authorities in whose care I was entrusted by the state, I could not approach them for help as this would have resulted in more harassment, therefore what I decided to do was to keep a record of the harassment I was experiencing in the hope that once outside I will be able to ask a lawyer or Panarama or media organization to do a story and request The Pentonville Prison Authorities to put a stop to the electronic harassment that they started, At present my case is with the Parliamentry Standards Ombudsman who have sent a complain note to the pentonville prison authority regarding their harassment against me, however The Parliamentry Ombudsman is request contact detail and story of other Prison Victim of voice to skull electronic harassment in order to complete their investigation which could lead to a parliament Law against Prison voice to skull electronic harassment therefore I would like to request all Prison victim of voice to skull electronic harassment to email me at [email protected] also I the undersign would like the help of Investigative Journlist also prison documentary editor media organization also voice to skull human right organization regarding investigating the note and do a story requesting The Pentonville Prison Authorities to put a stop to the electronic harassment that they started email me at email address above, as the pentonville prison authority are in receit of all document i.e signed support witness statement regarding my case also a legal undertaken requesting the above is sent on 10 June 2015 requesting them to stop their voice to skull electronic harassment against me however to date there is a lack of a response from the pentonville prison authority regarding the undertaken however media pressure to date has result in the Pentonville prison authority request prison document however further media pressure is needed to effect a stopping of the Pentonville voice to skull electronic harassment against me and all prison victim of voice to skull electronic harassment.
Contact Details
Name:Yaya Jawara
214 Stockfield Road
London E17 3LT
Tel :07947544914
Email address: [email protected]
Yours Sincerely
Yaya Jawara BSc Telecommunication And Computer Network
Email is send 17, 19, 21 July 2018 also 2 September 2018
Email is send 17, 18 July 2018
Dear Azuthor your help iis appreciated regarding
1: sign petition see petition link address bzelow
2: publish note and peppetition link address for for 3700 to sign at your fzacebook also meyour media Blog address also at your media Journalist czontact email address
3: state electronic Jzammer which is help regarding your voice to skull electronic hzarassment
Ezmail is sent 18, 24, 25, 28 June 2018 azlso 2, 3, 7, 10 July 2018
Dear Azuthor pzsytronic mzedia Tzitle aznd rzader which azshfak nzot nzormal electronic hzarassment regard is pzresent 7 hzour rzacial hzhzarassment aznd rzacial lzower bzack azbove sztate izs kzalf aznd ezlectronic hzarassment is ppzsytronic azshfak sztate Dzarkey azs sztate azbove fzor 7 hzour aznd Dzarkey izs nzote aznd lzogo wzhen nzormal ezlectronic hzatrassment szhould kzurcian mzale a wzhich nzot sztate this is rzacial hzarassment rzacial lzower bzack azs sztate aznd attachment azlso kzalf azshfak sztate kzalf this izs azlso rzacial lzower bzack azs sztate aznd attachment azlsoyour help is request regarding sign and parliamentry omboombudsman voice to skull electronic hzarassment petition see attachment for address ozr sign aznd note see attachment also state Ezlectronic Jzammer wzhich is hzelp regarding your voice to skull ezlectronic hzarassment also if you hzave szolution which could hzelp stop ozr Dzisrupt to grear ezxtent ezlectronicTzurture Tzarget tzhat could result aznd mze pzresent azt wzaitrow fzactory if you could state azbove request at czontact email address bzelow this would be appreciated also from ezlectronic rzeasearch Iz would lzike yzou tzo publish gzood bzelow azlso note szee attachment to your media azlso see link regard electronic gzood increase energy also good regarding hzealth also The MiniZAP® LCD is a Dr. Robert C. Beck Zapper and the world’s smallest yet most advanced blood zapper (blood purifier device) also The miniZAP® is a Dr . Robert C. Beck Zapper and the world’s smallest yet most advanced blood zapper (blood purifier device). The miniZAP® LCD energizes the body by weak alternating currents through the skin and strengthens its power and regenerative … also BECK ZAPPER (MINIZAPPER) | eBay
£ 289.99
BECK ZAPPER (MINIZAPPER) | eBay
German designed and built Beck Zapper (blood purifier device) now available in wrist watch fit for your comfort …
czontact address aznd email address to post and send your mzedia nzote wzhen request is:
Mr Yaya Jawara
214 Stocksfield Road
Walthamstow, London E17 3LT
Czontact Email address is : [email protected]
sign this petition if you are serious regarding stopping voice to skull electronic hzarassment also your help is appreciated
https://www.thepetitionsite.com/takeaction/884/885/181/
https://www.youtube.com/watch?v=0ldSaiY-BWA sztop szeperate kzen regard Yaya Jawara BSc Telecommunication
PS Please note that azs email bzelow is Az mzatter of urgency your quick response tzo email bzelow wzill bze appreciatedif serious regarding stopping voice to skull Ezlectronic hzarassment pzroblem yzour help is appreciated regarding sign aznd pzetition lzink address https://www.thepetitionsite.com/takeaction/884/885/181/ https://www.youtube.com/watch?v=0ldSaiY-BWA regard Yaya Jawara BSc TelecommunicationEzmail is sent 18, 24, 25, 28 June 2018 azlso 2, 3, 7 July 2018Dear Azuthor pzsytronic mzedia Tzitle aznd rzader which azshfak nzot nzormal electronic hzarassment regard is pzresent 7 hzour rzacial hzhzarassment aznd rzacial lzower bzack azbove sztate izs kzalf aznd ezlectronic hzarassment is ppzsytronic azshfak sztate Dzarkey azs sztate azbove fzor 7 hzour aznd Dzarkey izs nzote aznd lzogo wzhen nzormal ezlectronic hzatrassment szhould kzurcian mzale a wzhich nzot sztate this is rzacial hzarassment rzacial lzower bzack azs sztate aznd attachment azlso kzalf azshfak sztate kzalf this izs azlso rzacial lzower bzack azs sztate aznd attachment azlsoyour help is request regarding sign and parliamentry omboombudsman voice to skull electronic hzarassment petition see attachment for address ozr sign aznd note see attachment also state Ezlectronic Jzammer wzhich is hzelp regarding your voice to skull ezlectronic hzarassment also if you hzave szolution which could hzelp stop ozr Dzisrupt to grear ezxtent ezlectronicTzurture Tzarget tzhat could result aznd mze pzresent azt wzaitrow fzactory if you could state azbove request at czontact email address bzelow this would be appreciated also from ezlectronic rzeasearch Iz would lzike yzou tzo publish gzood bzelow azlso note szee attachment to your media azlso see link regard electronic gzood increase energy also good regarding hzealth also The MiniZAP® LCD is a Dr. Robert C. Beck Zapper and the world’s smallest yet most advanced blood zapper (blood purifier device) also The miniZAP® is a Dr . Robert C. Beck Zapper and the world’s smallest yet most advanced blood zapper (blood purifier device). The miniZAP® LCD energizes the body by weak alternating currents through the skin and strengthens its power and regenerative … also BECK ZAPPER (MINIZAPPER) | eBay £ 289.99 BECK ZAPPER (MINIZAPPER) | eBay German designed and built Beck Zapper (blood purifier device) now available in wrist watch fit for your comfort … czontact address aznd email address to post and send your mzedia nzote wzhen request is:Mr Yaya Jawara 214 Stocksfield RoadWalthamstow, London E17 3LTCzontact Email address is : [email protected] you are serious regarding stopping voice to skull Electronic hzarassment pzroblem your help is appreciated regarding sign pzetition address Bzelow https://www.thepetitionsite.com/takeaction/884/885/181/ https://www.youtube.com/watch?v=0ldSaiY-BWA regard Yaya Jawara BSc Telecommunication
czontact address aznd email address to post and send your mzedia nzote wzhen request is:
Mr Yaya Jawara
214 Stocksfield Road
Walthamstow, London E17 3LT
Czontact Email address is : [email protected]
if serious regarding stopping voice to skull EzlEEzEzlectronic hzarassment your help is appreciated regarding sign pzetition Lzink address see Bzelow
https://www.thepetitionsite.com/takeaction/884/885/181/ https://www.youtube.com/watch?v=0ldSaiY-BWA
https://www.thepetitionsite.com/takeaction/884/885/181/ https://www.youtube.com/watch?v=0ldSaiY-BWA regard Yaya Jawara BSc Telecommunication
Hi, I live in lower Michigan and have been gangstalked and v2k harassed for 9 months now. I\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\’ve had deaths threats against myself and my family if I dare speak out. I am trying to get the word out safely and scientifically because so many people of the general public have no knowledge or just dismiss my story and think I\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\’m crazy hearing voices. Not sure where to begin or who to address about this horrible no touch tourcher being done on innocent good hard working people.
Your not the only one …see Ramola D.
https://everydayconcerned.net
I’ve been a victim of voice to skull since 12/31/2020. Capri Nicole Warren is one of the Remote operaters of the voice to skull device. The operating system was located at 824 Mechanic Ave in Ravenna Ohio. I have more information about this. Please contact and let me know if you can help me.
Nice post! You have written useful and practical information. Take a look at my web blog Webemail24 I’m sure you’ll find supplementry information about Website Design you can gain new insights from.